实例介绍
【实例截图】
【核心代码】
目录
编者与作者介绍
主编致辞
前言
第 1 章 内核入门 ··························································1
HACK #1 如何获取 Linux 内核 ·········································································1
HACK #2 如何编译 Linux 内核 ·········································································7
HACK #3 如何编写内核模块 ··········································································18
HACK #4 如何使用 Git ··················································································22
HACK #5 使用 checkpatch.pl 检查补丁的格式 ···············································41
HACK #6 使用 localmodconfig 缩短编译时间 ·················································44
第 2 章 资源管理 ························································47
HACK #7 Cgroup、Namespace、Linux 容器 ················································47
HACK #8 调度策略 ·······················································································55
HACK #9 RT Group Scheduling 与 RT Throttling ··········································59
HACK #10 Fair Group Scheduling ································································62
HACK #11 cpuset ·························································································65
HACK #12 使用 Memory Cgroup 限制内存使用量 ··········································68
ii | 目 录
HACK #13 使用 Block I/O 控制器设置 I/O 优先级 ···········································74
HACK #14 虚拟存储子系统的调整 ·································································80
HACK #15 ramzswap ···················································································85
HACK #16 OOM Killer 的运行与结构 ·····························································91
第 3 章 文件系统 ························································98
HACK #17 如何使用 ext4 ··············································································98
HACK #18 向 ext4 转换···············································································101
HACK #19 ext4 的调整 ···············································································104
HACK #20 使用 fio 进行 I/O 的基准测试 ······················································· 111
HACK #21 FUSE ························································································ 118
第 4 章 网络 ·····························································121
HACK #22 如何控制网络的带宽 ··································································121
HACK #23 TUN/TAP 设备 ···········································································126
HACK #24 网桥设备 ···················································································129
HACK #25 VLAN ························································································133
HACK #26 bonding 驱动程序 ······································································136
HACK #27 Network Drop Monitor ·······························································141
第 5 章 虚拟化 ··························································147
HACK #28 如何使用 Xen ············································································147
HACK #29 如何使用 KVM ···········································································153
HACK #30 如何不使用 DVD 安装操作系统 ···················································159
HACK #31 更改虚拟 CPU 分配方法,提高性能 ············································161
HACK #32 如何使用 EPT 提高客户端操作系统的性能 ··································166
HACK #33 使用 IOMMU 提高客户端操作系统运行速度 ·································173
HACK #34 使用 IOMMU SR-IOV 提高客户端操作系统速度 ··························183
HACK #35 SR-IOV 带宽控制 ·······································································187
HACK #36 使用 KSM 节约内存····································································189
HACK #37 如何挂载客户端操作系统的磁盘··················································194
目 录 | iii
HACK #38 从客户端操作系统识别虚拟机环境 ··············································200
HACK #39 如何调试客户端操作系统 ····························································205
第 6 章 省电 ·····························································213
HACK #40 ACPI ·························································································213
HACK #41 使用 ACPI 的 S 状态 ··································································224
HACK #42 使用 CPU 省电(C、P 状态) ······················································226
HACK #43 PCI 设备的热插拔 ······································································236
HACK #44 虚拟环境下的省电 ······································································240
HACK #45 远程管理机器的电源 ··································································246
HACK #46 USB 的电力管理 ········································································251
HACK #47 显示器的省电 ·············································································254
HACK #48 通过网络设备节省电能 ·······························································260
HACK #49 关闭键盘的 LED 来省电 ·····························································263
HACK #50 PowerTOP ················································································269
HACK #51 硬盘的省电 ················································································276
第 7 章 调试 ·····························································282
HACK #52 SysRq 键 ···················································································282
HACK #53 使用 diskdump 提取内核崩溃转储 ···············································288
HACK #54 使用 Kdump 提取内核崩溃转储···················································293
HACK #55 崩溃测试 ···················································································297
HACK #56 IPMI 看门狗计时器 ·····································································299
HACK #57 NMI 看门狗计时器 ·····································································305
HACK #58 soft lockup ················································································307
HACK #59 crash 命令 ·················································································312
HACK #60 核心转储过滤器 ·········································································326
HACK #61 生成用户模式进程的进程核心转储 ··············································329
HACK #62 使用 lockdep 查找系统的死锁 ·····················································335
HACK #63 检测内核的内存泄漏 ··································································341
iv | 目 录
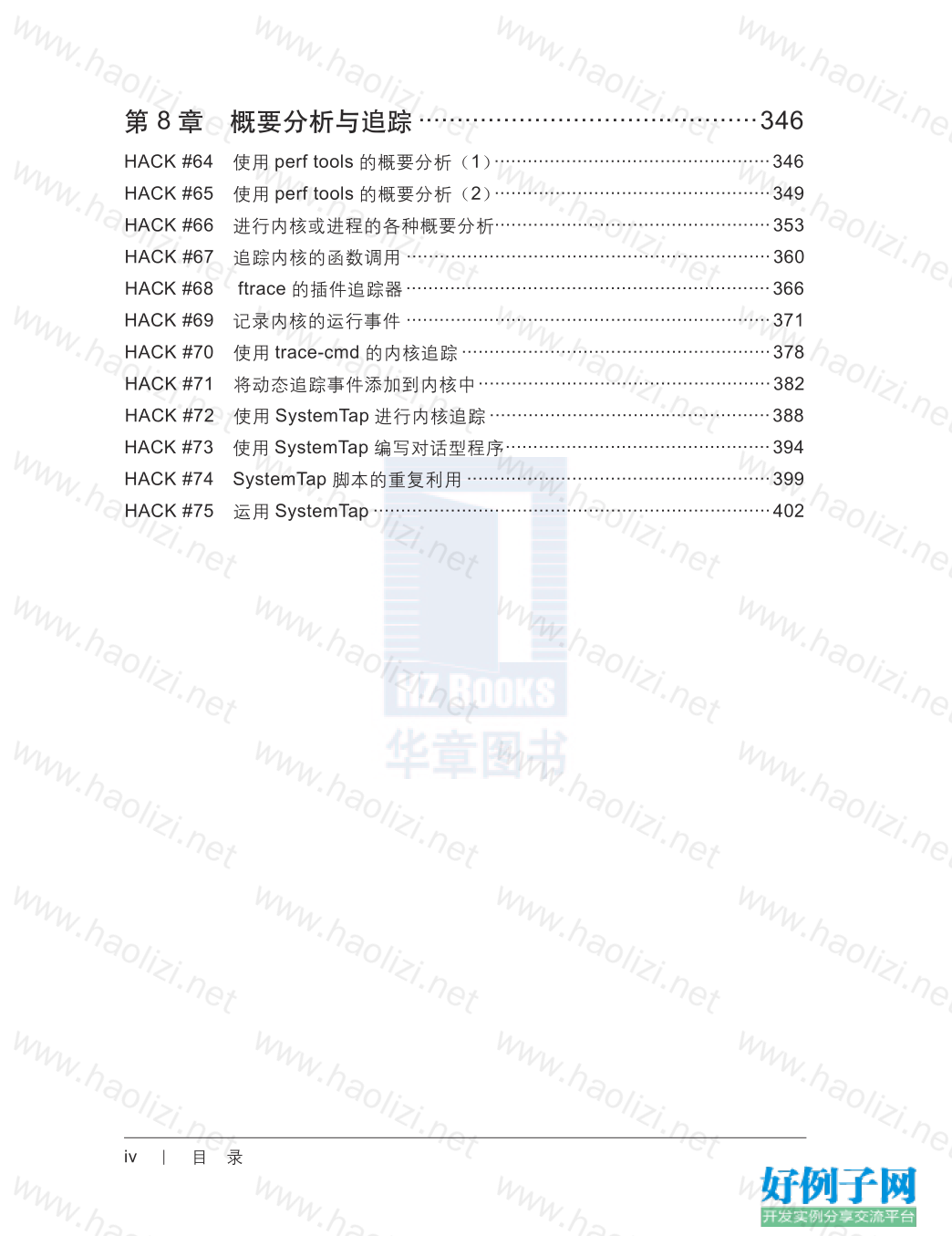
第 8 章 概要分析与追踪 ············································346
HACK #64 使用 perf tools 的概要分析(1) ··················································346
HACK #65 使用 perf tools 的概要分析(2) ··················································349
HACK #66 进行内核或进程的各种概要分析··················································353
HACK #67 追踪内核的函数调用 ··································································360
HACK #68 ftrace 的插件追踪器 ··································································366
HACK #69 记录内核的运行事件 ··································································371
HACK #70 使用 trace-cmd 的内核追踪 ························································378
HACK #71 将动态追踪事件添加到内核中 ·····················································382
HACK #72 使用 SystemTap 进行内核追踪 ···················································388
HACK #73 使用 SystemTap 编写对话型程序 ················································394
HACK #74 SystemTap 脚本的重复利用 ·······················································399
HACK #75 运用 SystemTap ········································································402
小贴士
感谢您为本站写下的评论,您的评论对其它用户来说具有重要的参考价值,所以请认真填写。
- 类似“顶”、“沙发”之类没有营养的文字,对勤劳贡献的楼主来说是令人沮丧的反馈信息。
- 相信您也不想看到一排文字/表情墙,所以请不要反馈意义不大的重复字符,也请尽量不要纯表情的回复。
- 提问之前请再仔细看一遍楼主的说明,或许是您遗漏了。
- 请勿到处挖坑绊人、招贴广告。既占空间让人厌烦,又没人会搭理,于人于己都无利。
关于好例子网
本站旨在为广大IT学习爱好者提供一个非营利性互相学习交流分享平台。本站所有资源都可以被免费获取学习研究。本站资源来自网友分享,对搜索内容的合法性不具有预见性、识别性、控制性,仅供学习研究,请务必在下载后24小时内给予删除,不得用于其他任何用途,否则后果自负。基于互联网的特殊性,平台无法对用户传输的作品、信息、内容的权属或合法性、安全性、合规性、真实性、科学性、完整权、有效性等进行实质审查;无论平台是否已进行审查,用户均应自行承担因其传输的作品、信息、内容而可能或已经产生的侵权或权属纠纷等法律责任。本站所有资源不代表本站的观点或立场,基于网友分享,根据中国法律《信息网络传播权保护条例》第二十二与二十三条之规定,若资源存在侵权或相关问题请联系本站客服人员,点此联系我们。关于更多版权及免责申明参见 版权及免责申明



网友评论
我要评论