实例介绍
【实例截图】
【核心代码】
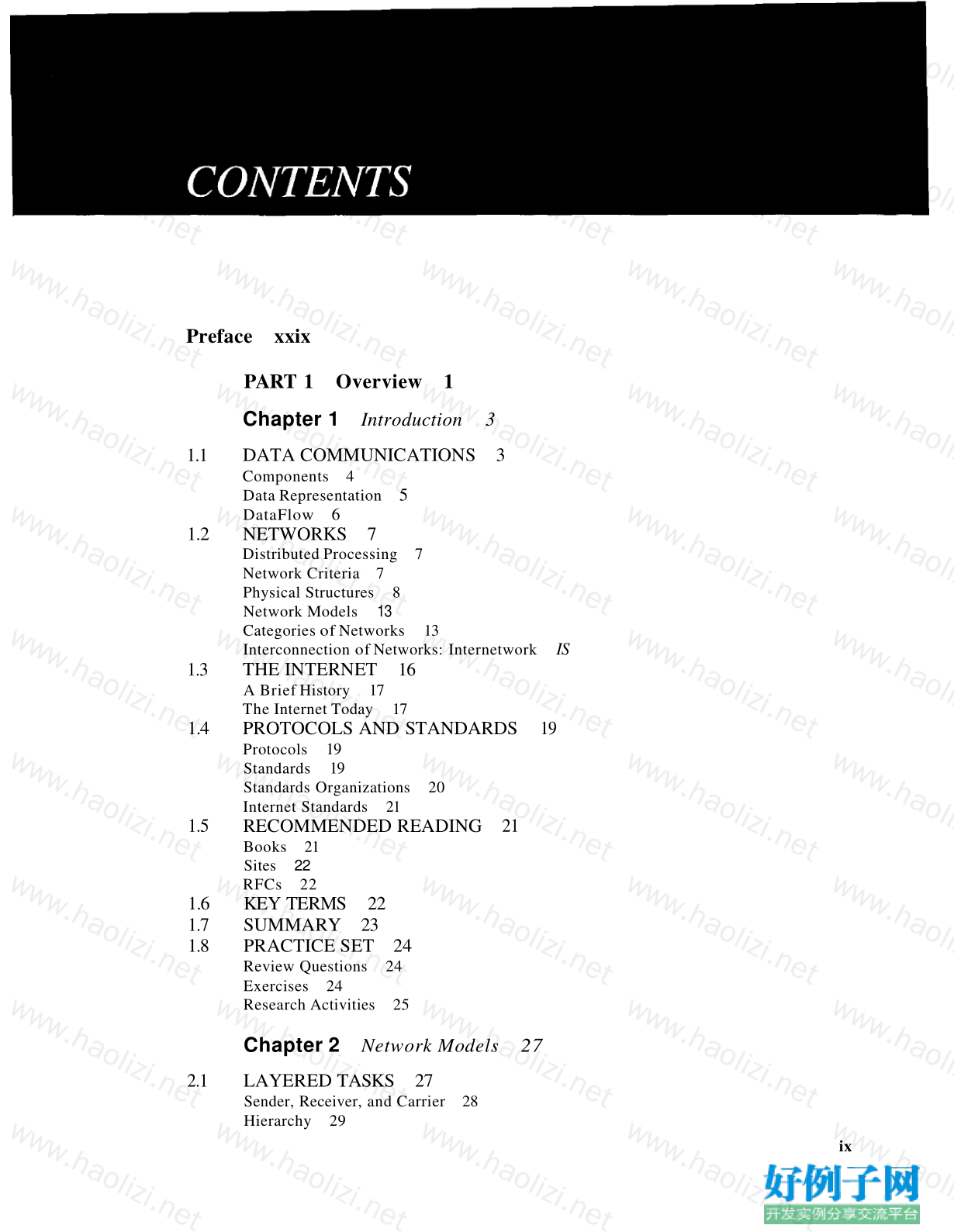
Preface xxix
PART 1 Overview 1
Chapter 1 Introduction 3
1.1 DATA COMMUNICATIONS 3
Components 4
Data Representation 5
DataFlow 6
1.2 NETWORKS 7
Distributed Processing 7
Network Criteria 7
Physical Structures 8
Network Models 13
Categories of Networks 13
Interconnection of Networks: Internetwork IS
1.3 THE INTERNET 16
A Brief History 17
The Internet Today 17
1.4 PROTOCOLS AND STANDARDS 19
Protocols 19
Standards 19
Standards Organizations 20
Internet Standards 21
1.5 RECOMMENDED READING 21
Books 21
Sites 22
RFCs 22
1.6 KEY TERMS 22
1.7 SUMMARY 23
1.8 PRACTICE SET 24
Review Questions 24
Exercises 24
Research Activities 25
Chapter 2 Network Models 27
2.1 LAYERED TASKS 27
Sender, Receiver, and Carrier 28
Hierarchy 29
ix
x CONTENTS
2.2 THE OSI MODEL 29
Layered Architecture 30
Peer-to-Peer Processes 30
Encapsulation 33
2.3 LAYERS IN THE OSI MODEL 33
Physical Layer 33
Data Link Layer 34
Network Layer 36
Transport Layer 37
Session Layer 39
Presentation Layer 39
Application Layer 41
Summary of Layers 42
2.4 TCP/IP PROTOCOL SUITE 42
Physical and Data Link Layers 43
Network Layer 43
Transport Layer 44
Application Layer 45
2.5 ADDRESSING 45
Physical Addresses 46
Logical Addresses 47
Port Addresses 49
Specific Addresses 50
2.6 RECOMMENDED READING 50
Books 51
Sites 51
RFCs 51
2.7 KEY lERMS 51
2.8 SUMMARY 52
2.9 PRACTICE SET 52
Review Questions 52
Exercises 53
Research Activities 54
PART 2 Physical Layer and Media 55
Chapter 3 Data and Signals 57
3.1 ANALOG AND DIGITAL 57
Analog and Digital Data 57
Analog and Digital Signals 58
Periodic and Nonperiodic Signals 58
3.2 PERIODIC ANALOG SIGNALS 59
Sine Wave 59
Phase 63
Wavelength 64
Time and Frequency Domains 65
Composite Signals 66
Bandwidth 69
3.3 DIGITAL SIGNALS 71
Bit Rate 73
Bit Length 73
Digital Signal as a Composite Analog Signal 74
Transmission of Digital Signals 74
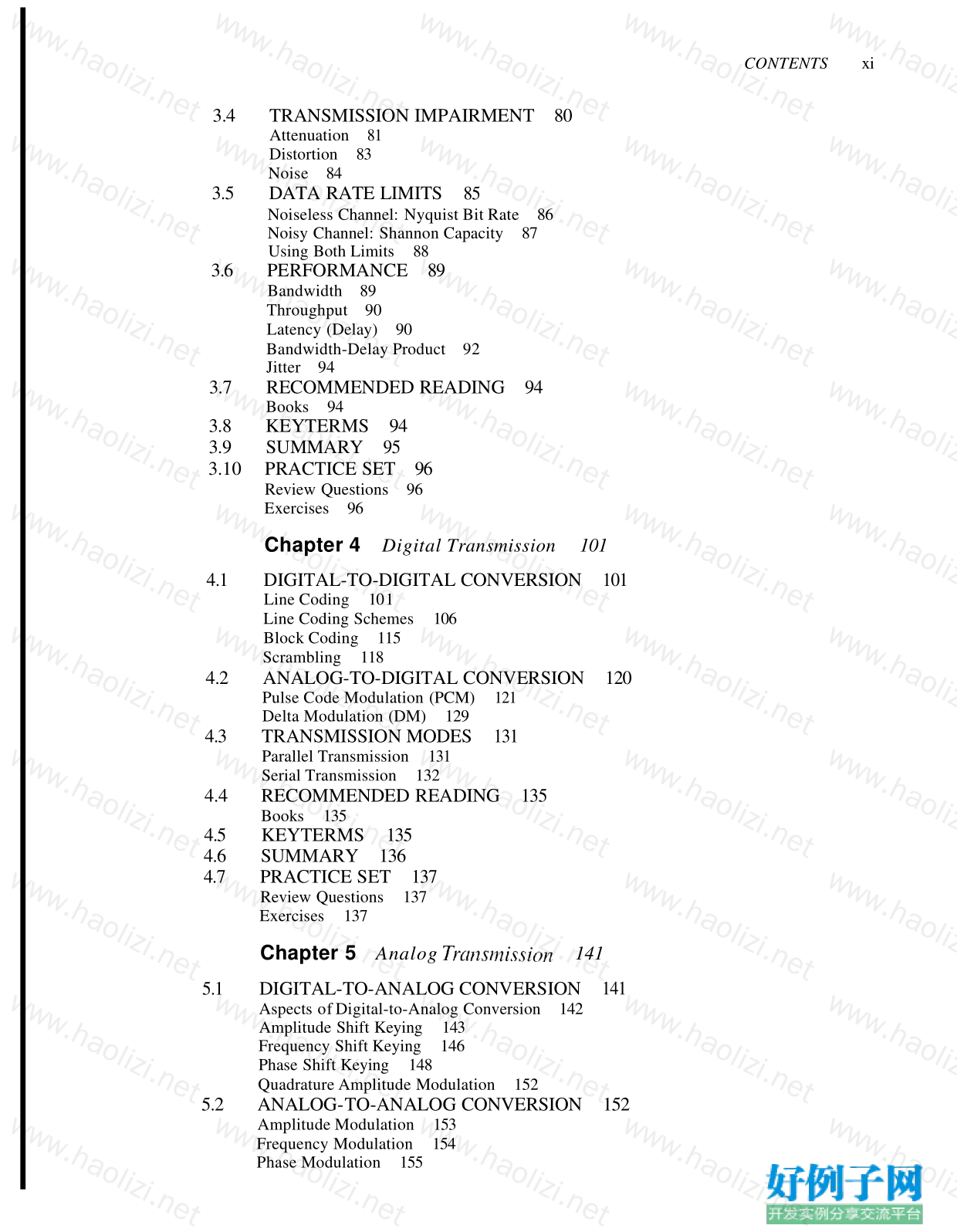
3.4 TRANSMISSION IMPAIRMENT 80
Attenuation 81
Distortion 83
Noise 84
3.5 DATA RATE LIMITS 85
Noiseless Channel: Nyquist Bit Rate 86
Noisy Channel: Shannon Capacity 87
Using Both Limits 88
3.6 PERFORMANCE 89
Bandwidth 89
Throughput 90
Latency (Delay) 90
Bandwidth-Delay Product 92
Jitter 94
3.7 RECOMMENDED READING 94
Books 94
3.8 KEYTERMS 94
3.9 SUMMARY 95
3.10 PRACTICE SET 96
Review Questions 96
Exercises 96
Chapter 4 Digital Transmission 101
4.1 DIGITAL-TO-DIGITAL CONVERSION 101
Line Coding 10 1
Line Coding Schemes 106
Block Coding 115
Scrambling 118
4.2 ANALOG-TO-DIGITAL CONVERSION 120
Pulse Code Modulation (PCM) 121
Delta Modulation (DM) 129
4.3 TRANSMISSION MODES 131
Parallel Transmission 131
Serial Transmission 132
4.4 RECOMMENDED READING 135
Books 135
4.5 KEYTERMS 135
4.6 SUMMARY 136
4.7 PRACTICE SET 137
Review Questions 137
Exercises 137
Chapter 5 Analog TranSl1'lission 141
5.1 DIGITAL-TO-ANALOG CONVERSION 141
Aspects of Digital-to-Analog Conversion 142
Amplitude Shift Keying 143
Frequency Shift Keying 146
Phase Shift Keying 148
Quadrature Amplitude Modulation 152
5.2 ANALOG-TO-ANALOG CONVERSION 152
Amplitude Modulation 153
Frequency Modulation 154
Phase Modulation 155
CONTENTS xi
xii CONTENTS
5.3 RECOMMENDED READING 156
Books 156
5.4 KEY lERMS 157
5.5 SUMMARY 157
5.6 PRACTICE SET 158
Review Questions 158
Exercises 158
Chapter 6 Ba17chridth Utili::.ation: Multiplexing
and Spreading 161
6.1 MULTIPLEXING 161
Frequency-Division Multiplexing 162
Wavelength-Division Multiplexing 167
Synchronous Time-Division Multiplexing 169
Statistical Time-Division Multiplexing 179
6.2 SPREAD SPECTRUM 180
Frequency Hopping Spread Spectrum (FHSS) 181
Direct Sequence Spread Spectrum 184
6.3 RECOMMENDED READING 185
Books 185
6.4 KEY lERMS 185
6.5 SUMMARY 186
6.6 PRACTICE SET 187
Review Questions 187
Exercises 187
Chapter 7 Transmission Media 191
7.1 GUIDED MEDIA 192
Twisted-Pair Cable 193
Coaxial Cable 195
Fiber-Optic Cable 198
7.2 UNGUIDED MEDIA: WIRELESS 203
Radio Waves 205
Microwaves 206
Infrared 207
7.3 RECOMMENDED READING 208
Books 208
7.4 KEY lERMS 208
7.5 SUMMARY 209
7.6 PRACTICE SET 209
Review Questions 209
Exercises 210
Chapter 8 Svvitching 213
8.1 CIRCUIT-SWITCHED NETWORKS 214
Three Phases 217
Efficiency 217
Delay 217
Circuit-Switched Technology in Telephone Networks 218
8.2 DATAGRAM NETWORKS 218
Routing Table 220
CONTENTS xiii
Efficiency 220
Delay 221
Datagram Networks in the Internet 221
8.3 VIRTUAL-CIRCUIT NETWORKS 221
Addressing 222
Three Phases 223
Efficiency 226
Delay in Virtual-Circuit Networks 226
Circuit-Switched Technology in WANs 227
8.4 STRUCTURE OF A SWITCH 227
Structure of Circuit Switches 227
Structure of Packet Switches 232
8.5 RECOMMENDED READING 235
Books 235
8.6 KEY TERMS 235
8.7 SUMMARY 236
8.8 PRACTICE SET 236
Review Questions 236
Exercises 237
Chapter 9 Using Telephone and Cable Networks for Data
Transm,ission 241
9.1 1ELEPHONE NETWORK 241
Major Components 241
LATAs 242
Signaling 244
Services Provided by Telephone Networks 247
9.2 DIAL-UP MODEMS 248
Modem Standards 249
9.3 DIGITAL SUBSCRIBER LINE 251
ADSL 252
ADSL Lite 254
HDSL 255
SDSL 255
VDSL 255
Summary 255
9.4 CABLE TV NETWORKS 256
Traditional Cable Networks 256
Hybrid Fiber-Coaxial (HFC) Network 256
9.5 CABLE TV FOR DATA TRANSFER 257
Bandwidth 257
Sharing 259
CM and CMTS 259
Data Transmission Schemes: DOCSIS 260
9.6 RECOMMENDED READING 261
Books 261
9.7 KEY TERMS 261
9.8 SUMMARY 262
9.9 PRACTICE SET 263
Review Questions 263
Exercises 264
xiv CONTENTS
PART 3 Data Link Layer 265
Chapter 10 Error Detection and Correction 267
10.1 INTRODUCTION 267
Types of Errors 267
Redundancy 269
Detection Versus Correction 269
Forward Error Correction Versus Retransmission 269
Coding 269
Modular Arithmetic 270
10.2 BLOCK CODING 271
Error Detection 272
Error Correction 273
Hamming Distance 274
Minimum Hamming Distance 274
10.3 LINEAR BLOCK CODES 277
Minimum Distance for Linear Block Codes 278
Some Linear Block Codes 278
10.4 CYCLIC CODES 284
Cyclic Redundancy Check 284
Hardware Implementation 287
Polynomials 291
Cyclic Code Analysis 293
Advantages of Cyclic Codes 297
Other Cyclic Codes 297
10.5 CHECKSUM 298
Idea 298
One's Complement 298
Internet Checksum 299
10.6 RECOMMENDED READING 30I
Books 301
RFCs 301
10.7 KEY lERMS 301
10.8 SUMMARY 302
10.9 PRACTICE SET 303
Review Questions 303
Exercises 303
Chapter 11 Data Link Control 307
11.1 FRAMING 307
Fixed-Size Framing 308
Variable-Size Framing 308
11.2 FLOW AND ERROR CONTROL 311
Flow Control 311
Error Control 311
11.3 PROTOCOLS 311
11.4 NOISELESS CHANNELS 312
Simplest Protocol 312
Stop-and-Wait Protocol 315
11.5 NOISY CHANNELS 318
Stop-and-WaitAutomatic Repeat Request 318
Go-Back-N Automatic Repeat Request 324
11.6
11.7
11.8
11.9
11.10
11.11
Selective Repeat Automatic Repeat Request
Piggybacking 339
HDLC 340
Configurations and Transfer Modes 340
Frames 341
Control Field 343
POINT-TO-POINT PROTOCOL 346
Framing 348
Transition Phases 349
Multiplexing 350
Multilink PPP 355
RECOMMENDED READING 357
Books 357
KEY TERMS 357
SUMMARY 358
PRACTICE SET 359
Review Questions 359
Exercises 359
332
CONTENTS xv
Chapter 12 Multiple Access 363
12.1 RANDOMACCESS 364
ALOHA 365
Carrier Sense Multiple Access (CSMA) 370
Carrier Sense Multiple Access with Collision Detection (CSMAlCD) 373
Carrier Sense Multiple Access with Collision Avoidance (CSMAlCA) 377
12.2 CONTROLLED ACCESS 379
Reservation 379
Polling 380
Token Passing 381
12.3 CHANNELIZATION 383
Frequency-Division Multiple Access (FDMA) 383
Time-Division Multiple Access (TDMA) 384
Code-Division Multiple Access (CDMA) 385
12.4 RECOMMENDED READING 390
Books 391
12.5 KEY TERMS 391
12.6 SUMMARY 391
12.7 PRACTICE SET 392
Review Questions 392
Exercises 393
Research Activities 394
Chapter 13 Wired LANs: Ethernet 395
13.1 IEEE STANDARDS 395
Data Link Layer 396
Physical Layer 397
13.2 STANDARD ETHERNET 397
MAC Sublayer 398
Physical Layer 402
13.3 CHANGES IN THE STANDARD 406
Bridged Ethernet 406
Switched Ethernet 407
Full-Duplex Ethernet 408
xvi CONTENTS
13.4 FAST ETHERNET 409
MAC Sublayer 409
Physical Layer 410
13.5 GIGABIT ETHERNET 412
MAC Sublayer 412
Physical Layer 414
Ten-Gigabit Ethernet 416
13.6 RECOMMENDED READING 417
Books 417
13.7 KEY TERMS 417
13.8 SUMMARY 417
13.9 PRACTICE SET 418
Review Questions 418
Exercises 419
Chapter 14 Wireless LANs 421
14.1 IEEE 802.11 421
Architecture 421
MAC Sublayer 423
Addressing Mechanism 428
Physical Layer 432
14.2 BLUETOOTH 434
Architecture 435
Bluetooth Layers 436
Radio Layer 436
Baseband Layer 437
L2CAP 440
Other Upper Layers 441
14.3 RECOMMENDED READING 44I
Books 442
14.4 KEYTERMS 442
14.5 SUMMARY 442
14.6 PRACTICE SET 443
Review Questions 443
Exercises 443
Chapter 15 Connecting LANs, Backbone Networks,
and VirtuaL LANs 445
15.1 CONNECTING DEVICES 445
Passive Hubs 446
Repeaters 446
Active Hubs 447
Bridges 447
Two-Layer Switches 454
Routers 455
Three-Layer Switches 455
Gateway 455
15.2 BACKBONE NETWORKS 456
Bus Backbone 456
Star Backbone 457
Connecting Remote LANs 457
15.3 VIRTUAL LANs 458
Membership 461
Configuration 461
Communication Between Switches 462
IEEE Standard 462
Advantages 463
15.4 RECOMMENDED READING 463
Books 463
Site 463
15.5 KEY TERMS 463
15.6 SUMMARY 464
15.7 PRACTICE SET 464
Review Questions 464
Exercises 465
CONTENTS xvii
Chapter 16 Wireless WANs: Cellular Telephone and
Satellite Networks 467
16.1 CELLULAR TELEPHONY 467
Frequency-Reuse Principle 467
Transmitting 468
Receiving 469
Roaming 469
First Generation 469
Second Generation 470
Third Generation 477
16.2 SATELLITE NETWORKS 478
Orbits 479
Footprint 480
Three Categories of Satellites 480
GEO Satellites 481
MEO Satellites 481
LEO Satellites 484
16.3 RECOMMENDED READING 487
Books 487
16.4 KEY TERMS 487
16.5 SUMMARY 487
16.6 PRACTICE SET 488
Review Questions 488
Exercises 488
Chapter 17 SONETISDH 491
17.1 ARCHITECTURE 491
Signals 491
SONET Devices 492
Connections 493
17.2 SONET LAYERS 494
Path Layer 494
Line Layer 495
Section Layer 495
Photonic Layer 495
Device-Layer Relationships 495
xviii CONTENTS
17.3 SONET FRAMES 496
Frame, Byte, and Bit Transmission 496
STS-l Frame Format 497
Overhead Summary 501
Encapsulation 501
17.4 STS MULTIPLEXING 503
Byte Interleaving 504
Concatenated Signal 505
AddlDrop Multiplexer 506
17.5 SONET NETWORKS 507
Linear Networks 507
Ring Networks 509
Mesh Networks 510
17.6 VIRTUAL TRIBUTARIES 512
Types ofVTs 512
17.7 RECOMMENDED READING 513
Books 513
17.8 KEY lERMS 513
17.9 SUMMARY 514
17.1 0 PRACTICE SET 514
Review Questions 514
Exercises 515
Chapter 18 Virtual-Circuit Networks: Frame Relm' and ATM 517
18.1 FRAME RELAY 517
Architecture 518
Frame Relay Layers 519
Extended Address 521
FRADs 522
VOFR 522
LMI 522
Congestion Control and Quality of Service 522
18.2 ATM 523
Design Goals 523
Problems 523
Architecture 526
Switching 529
ATM Layers 529
Congestion Control and Quality of Service 535
18.3 ATM LANs 536
ATM LAN Architecture 536
LAN Emulation (LANE) 538
Client/Server Model 539
Mixed Architecture with Client/Server 540
18.4 RECOMMENDED READING 540
Books 541
18.5 KEY lERMS 541
18.6 SUMMARY 541
18.7 PRACTICE SET 543
Review Questions 543
Exercises 543
CONTENTS xix
PART 4 Network Layer 547
Chapter 19 Netvl/ark Layer: Logical Addressing 549
19.1 IPv4ADDRESSES 549
Address Space 550
Notations 550
Classful Addressing 552
Classless Addressing 555
NetworkAddress Translation (NAT) 563
19.2 IPv6 ADDRESSES 566
Structure 567
Address Space 568
19.3 RECOMMENDED READING 572
Books 572
Sites 572
RFCs 572
19.4 KEY TERMS 572
19.5 SUMMARY 573
19.6 PRACTICE SET 574
Review Questions 574
Exercises 574
Research Activities 577
Chapter 20 Network Layer: Internet Protocol 579
20.1 INTERNETWORKING 579
Need for Network Layer 579
Internet as a Datagram Network 581
Internet as a Connectionless Network 582
20.2 IPv4 582
Datagram 583
Fragmentation 589
Checksum 594
Options 594
20.3 IPv6 596
Advantages 597
Packet Format 597
Extension Headers 602
20.4 TRANSITION FROM IPv4 TO IPv6 603
Dual Stack 604
Tunneling 604
Header Translation 605
20.5 RECOMMENDED READING 605
Books 606
Sites 606
RFCs 606
20.6 KEY TERMS 606
20.7 SUMMARY 607
20.8 PRACTICE SET 607
Review Questions 607
Exercises 608
Research Activities 609
xx CONTENTS
Chapter 21 Network Layer: Address Mapping, Error Reporting,
and Multicasting 611
21.1 ADDRESS MAPPING 611
Mapping Logical to Physical Address: ARP 612
Mapping Physical to Logical Address: RARp, BOOTP, and DHCP 618
21.2 ICMP 621
Types of Messages 621
Message Format 621
Error Reporting 622
Query 625
Debugging Tools 627
21.3 IGMP 630
Group Management 630
IGMP Messages 631
Message Format 631
IGMP Operation 632
Encapsulation 635
Netstat Utility 637
21.4 ICMPv6 638
Error Reporting 638
Query 639
21.5 RECOMMENDED READING 640
Books 641
Site 641
RFCs 641
21.6 KEYTERMS 641
21.7 SUMMARY 642
21.8 PRACTICE SET 643
Review Questions 643
Exercises 644
Research Activities 645
Chapter 22 Network Layer: Delivery, Forwarding,
and Routing 647
22.1 DELIVERY 647
Direct Versus Indirect Delivery 647
22.2 FORWARDING 648
Forwarding Techniques 648
Forwarding Process 650
Routing Table 655
22.3 UNICAST ROUTING PROTOCOLS 658
Optimization 658
Intra- and Interdomain Routing 659
Distance Vector Routing 660
Link State Routing 666
Path Vector Routing 674
22.4 MULTICAST ROUTING PROTOCOLS 678
Unicast, Multicast, and Broadcast 678
Applications 681
Multicast Routing 682
Routing Protocols 684
CONTENTS xxi
22.5 RECOMMENDED READING 694
Books 694
Sites 694
RFCs 694
22.6 KEY lERMS 694
22.7 SUMMARY 695
22.8 PRACTICE SET 697
Review Questions 697
Exercises 697
Research Activities 699
PART 5 Transport Layer 701
Chapter 23 Process-fa-Process Delivery: UDp, TCp,
and SeTP 703
23.1 PROCESS-TO-PROCESS DELIVERY 703
Client/Server Paradigm 704
Multiplexing and Demultiplexing 707
Connectionless Versus Connection-Oriented Service 707
Reliable Versus Unreliable 708
Three Protocols 708
23.2 USER DATAGRAM PROTOCOL (UDP) 709
Well-Known Ports for UDP 709
User Datagram 710
Checksum 711
UDP Operation 713
Use ofUDP 715
23.3 TCP 715
TCP Services 715
TCP Features 719
Segment 721
A TCP Connection 723
Flow Control 728
Error Control 731
Congestion Control 735
23.4 SCTP 736
SCTP Services 736
SCTP Features 738
Packet Format 742
An SCTP Association 743
Flow Control 748
Error Control 751
Congestion Control 753
23.5 RECOMMENDED READING 753
Books 753
Sites 753
RFCs 753
23.6 KEY lERMS 754
23.7 SUMMARY 754
23.8 PRACTICE SET 756
Review Questions 756
Exercises 757
Research Activities 759
xxii CONTENTS
Chapter 24 Congestion Control and Quality ( ~ j ' S e r v i c e 767
24.1 DATA lRAFFIC 761
Traffic Descriptor 76]
Traffic Profiles 762
24.2 CONGESTION 763
Network Performance 764
24.3 CONGESTION CONTROL 765
Open-Loop Congestion Control 766
Closed-Loop Congestion Control 767
24.4 lWO EXAMPLES 768
Congestion Control in TCP 769
Congestion Control in Frame Relay 773
24.5 QUALITY OF SERVICE 775
Flow Characteristics 775
Flow Classes 776
24.6 TECHNIQUES TO IMPROVE QoS 776
Scheduling 776
Traffic Shaping 777
Resource Reservation 780
Admission Control 780
24.7 INTEGRATED SERVICES 780
Signaling 781
Flow Specification 781
Admission 781
Service Classes 781
RSVP 782
Problems with Integrated Services 784
24.8 DIFFERENTIATED SERVICES 785
DS Field 785
24.9 QoS IN SWITCHED NETWORKS 786
QoS in Frame Relay 787
QoS inATM 789
24.10 RECOMMENDED READING 790
Books 791
24.11 KEY TERMS 791
24.12 SUMMARY 791
24.13 PRACTICE SET 792
Review Questions 792
Exercises 793
PART 6 Application Layer 795
Chapter 25 DO/nain Name Svstem 797
25.1 NAME SPACE 798
Flat Name Space 798
Hierarchical Name Space 798
25.2 DOMAIN NAME SPACE 799
Label 799
Domain Narne 799
Domain 801
25.3
25.4
25.5
25.6
25.7
25.8
25.9
25.10
25.11
25.12
25.13
25.14
DISTRIBUTION OF NAME SPACE 801
Hierarchy of Name Servers 802
Zone 802
Root Server 803
Primary and Secondary Servers 803
DNS IN THE INTERNET 803
Generic Domains 804
Country Domains 805
Inverse Domain 805
RESOLUTION 806
Resolver 806
Mapping Names to Addresses 807
Mapping Address to Names 807
Recursive Resolution 808
Iterative Resolution 808
Caching 808
DNS MESSAGES 809
Header 809
TYPES OF RECORDS 811
Question Record 811
Resource Record 811
REGISTRARS 811
DYNAMIC DOMAIN NAME SYSTEM (DDNS)
ENCAPSULATION 812
RECOMMENDED READING 812
Books 813
Sites 813
RFCs 813
KEY TERMS 813
SUMMARY 813
PRACTICE SET 814
Review Questions 814
Exercises 815
812
CONTENTS xxiii
Chapter 26 Remote Logging, Electronic Mail, and File Transfer 817
26.1 REMOTE LOGGING 817
TELNET 817
26.2 ELECTRONIC MAIL 824
Architecture 824
User Agent 828
Message TransferAgent: SMTP 834
Message Access Agent: POP and IMAP 837
Web-Based Mail 839
26.3 FILE TRANSFER 840
File Transfer Protocol (FTP) 840
Anonymous FTP 844
26.4 RECOMMENDED READING 845
Books 845
Sites 845
RFCs 845
26.5 KEY lERMS 845
26.6 SUMMARY 846
xxiv CONTENTS
26.7 PRACTICE SET 847
Review Questions 847
Exercises 848
Research Activities 848
Chapter 27 WWW and HTTP 851
27.1 ARCHITECTURE 851
Client (Browser) 852
Server 852
Uniform Resource Locator 853
Cookies 853
27.2 WEB DOCUMENTS 854
Static Documents 855
Dynamic Documents 857
Active Documents 860
27.3 HTTP 861
HTTP Transaction 861
Persistent Versus Nonpersistent Connection 868
Proxy Server 868
27.4 RECOMMENDED READING 869
Books 869
Sites 869
RFCs 869
27.5 KEY 1ERMS 869
27.6 SUMMARY 870
27.7 PRACTICE SET 871
Review Questions 871
Exercises 871
Chapter 28 Network Management: SNMP 873
28.1 NETWORK MANAGEMENT SYSTEM 873
Configuration Management 874
Fault Management 875
Performance Management 876
Security Management 876
Accounting Management 877
28.2 SIMPLE NETWORK MANAGEMENT PROTOCOL (SNMP) 877
Concept 877
Management Components 878
Structure of Management Information 881
Management Information Base (MIB) 886
Lexicographic Ordering 889
SNMP 891
Messages 893
UDP Ports 895
Security 897
28.3 RECOMMENDED READING 897
Books 897
Sites 897
RFCs 897
28.4 KEY 1ERMS 897
28.5 SUMMARY 898
28.6 PRACTICE SET 899
Review Questions 899
Exercises 899
Chapter 29 Multimedia 901
29.1 DIGITIZINGAUDIO AND VIDEO 902
Digitizing Audio 902
Digitizing Video 902
29.2 AUDIO AND VIDEO COMPRESSION 903
Audio Compression 903
Video Compression 904
29.3 STREAMING STORED AUDIO/VIDEO 908
FirstApproach: Using aWeb Server 909
Second Approach: Using a Web Server with Metafile 909
Third Approach: Using a Media Server 910
Fourth Approach: Using a Media Server and RTSP 911
29.4 STREAMING LIVE AUDIOIVIDEO 912
29.5 REAL-TIME INTERACTIVE AUDIOIVIDEO 912
Characteristics 912
29.6 RTP 916
RTP Packet Format 917
UDPPort 919
29.7 RTCP 919
Sender Report 919
Receiver Report 920
Source Description Message 920
Bye Message 920
Application-Specific Message 920
UDP Port 920
29.8 VOICE OVER IP 920
SIP 920
H.323 923
29.9 RECOMMENDED READING 925
Books 925
Sites 925
29.10 KEY 1ERMS 925
29.11 SUMMARY 926
29.12 PRACTICE SET 927
Review Questions 927
Exercises 927
Research Activities 928
PART 7 Security 929
Chapter 30 Cryptography 931
30.1 INTRODUCTION 931
Definitions 931
Two Categories 932
30.2 SYMMETRIC-KEY CRYPTOGRAPHY 935
Traditional Ciphers 935
Simple Modem Ciphers 938
CONTENTS xxv
xxvi CONTENTS
Modern Round Ciphers 940
Mode of Operation 945
30.3 ASYMMETRIC-KEY CRYPTOGRAPHY 949
RSA 949
Diffie-Hellman 952
30.4 RECOMMENDED READING 956
Books 956
30.5 KEY TERMS 956
30.6 SUMMARY 957
30.7 PRACTICE SET 958
Review Questions 958
Exercises 959
Research Activities 960
Chapter 31 Network Security 961
31.1 SECURITY SERVICES 961
Message Confidentiality 962
Message Integrity 962
Message Authentication 962
Message Nonrepudiation 962
Entity Authentication 962
31.2 MESSAGE CONFIDENTIALITY 962
Confidentiality with Symmetric-Key Cryptography 963
Confidentiality with Asymmetric-Key Cryptography 963
31.3 MESSAGE INTEGRITY 964
Document and Fingerprint 965
Message and Message Digest 965
Difference 965
Creating and Checking the Digest 966
Hash Function Criteria 966
Hash Algorithms: SHA-1 967
31.4 MESSAGE AUTHENTICATION 969
MAC 969
31.5 DIGITAL SIGNATURE 971
Comparison 97 I
Need for Keys 972
Process 973
Services 974
Signature Schemes 976
31.6 ENTITY AUTHENTICATION 976
Passwords 976
Challenge-Response 978
31.7 KEY MANAGEMENT 981
Symmetric-Key Distribution 981
Public-Key Distribution 986
31.8 RECOMMENDED READING 990
Books 990
31.9 KEY TERMS 990
31.10 SUMMARY 991
31.11 PRACTICE SET 992
Review Questions 992
Exercises 993
Research Activities 994
CONTENTS xxvii
Chapter 32 Security in the Internet: IPSec, SSUFLS, PGP, VPN,
and Firewalls 995
32.1 IPSecurity (lPSec) 996
Two Modes 996
Two Security Protocols 998
Security Association 1002
Internet Key Exchange (IKE) 1004
Virtual Private Network 1004
32.2 SSLffLS 1008
SSL Services 1008
Security Parameters 1009
Sessions and Connections 1011
Four Protocols 1012
Transport Layer Security 1013
32.3 PGP 1014
Security Parameters 1015
Services 1015
A Scenario 1016
PGP Algorithms 1017
Key Rings 1018
PGP Certificates 10 19
32.4 FIREWALLS 1021
Packet-Filter Firewall 1022
Proxy Firewall 1023
32.5 RECOMMENDED READING 1024
Books 1024
32.6 KEY lERMS 1024
32.7 SUMMARY 1025
32.8 PRACTICE SET 1026
Review Questions 1026
Exercises 1026
Appendix A Unicode 1029
A.l UNICODE 1029
Planes 1030
Basic Multilingual Plane (BMP) 1030
Supplementary Multilingual Plane (SMP) 1032
Supplementary Ideographic Plane (SIP) 1032
Supplementary Special Plane (SSP) 1032
Private Use Planes (PUPs) 1032
A.2 ASCII 1032
Some Properties of ASCII 1036
Appendix B Numbering Systems 1037
B.l BASE 10: DECIMAL 1037
Weights 1038
B.2 BASE 2: BINARY 1038
Weights 1038
Conversion 1038
xxviii CONTENTS
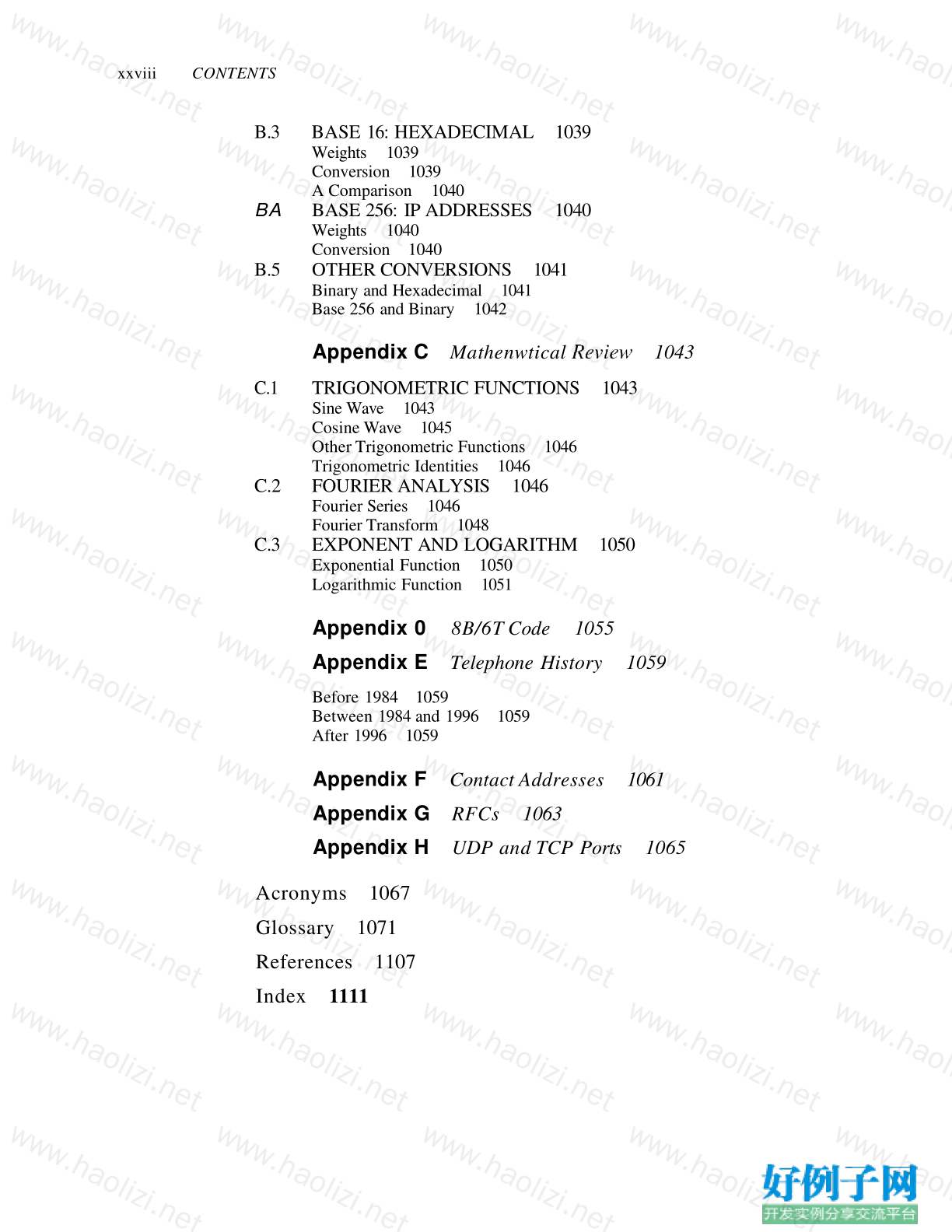
B.3 BASE 16: HEXADECIMAL 1039
Weights 1039
Conversion 1039
A Comparison 1040
BA BASE 256: IP ADDRESSES 1040
Weights 1040
Conversion 1040
B.5 OTHER CONVERSIONS 1041
Binary and Hexadecimal 1041
Base 256 and Binary 1042
Appendix C Mathenwtical Revietv 1043
C.1 TRIGONOMETRIC FUNCTIONS 1043
Sine Wave 1043
Cosine Wave 1045
Other Trigonometric Functions 1046
Trigonometric Identities 1046
C.2 FOURIER ANALYSIS 1046
Fourier Series 1046
Fourier Transform 1048
C.3 EXPONENT AND LOGARITHM 1050
Exponential Function 1050
Logarithmic Function 1051
Appendix 0 8B/6T Code 1055
Appendix E Telephone History 1059
Before 1984 1059
Between 1984 and 1996 1059
After 1996 1059
Appendix F Contact Addresses 1061
Appendix G RFCs 1063
Appendix H UDP and TCP Ports 1065
Acronyms 1067
Glossary 1071
References 1107
Index 1111
小贴士
感谢您为本站写下的评论,您的评论对其它用户来说具有重要的参考价值,所以请认真填写。
- 类似“顶”、“沙发”之类没有营养的文字,对勤劳贡献的楼主来说是令人沮丧的反馈信息。
- 相信您也不想看到一排文字/表情墙,所以请不要反馈意义不大的重复字符,也请尽量不要纯表情的回复。
- 提问之前请再仔细看一遍楼主的说明,或许是您遗漏了。
- 请勿到处挖坑绊人、招贴广告。既占空间让人厌烦,又没人会搭理,于人于己都无利。
关于好例子网
本站旨在为广大IT学习爱好者提供一个非营利性互相学习交流分享平台。本站所有资源都可以被免费获取学习研究。本站资源来自网友分享,对搜索内容的合法性不具有预见性、识别性、控制性,仅供学习研究,请务必在下载后24小时内给予删除,不得用于其他任何用途,否则后果自负。基于互联网的特殊性,平台无法对用户传输的作品、信息、内容的权属或合法性、安全性、合规性、真实性、科学性、完整权、有效性等进行实质审查;无论平台是否已进行审查,用户均应自行承担因其传输的作品、信息、内容而可能或已经产生的侵权或权属纠纷等法律责任。本站所有资源不代表本站的观点或立场,基于网友分享,根据中国法律《信息网络传播权保护条例》第二十二与二十三条之规定,若资源存在侵权或相关问题请联系本站客服人员,点此联系我们。关于更多版权及免责申明参见 版权及免责申明



网友评论
我要评论